Team PC Puts Malware in Backdoored Telnyx Packages via WAV Files
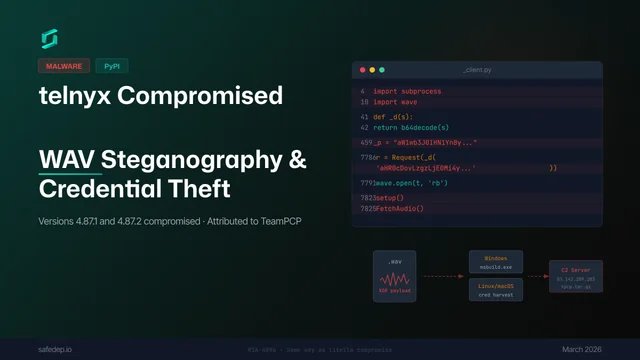
On March 27, threat actor TeamPCP compromised the Telnyx Python package by uploading two malicious versions (4.87.1 and 4.87.2) directly to PyPI that deliver credential-stealing malware hidden inside WAV audio files using steganography; this supply chain attack targets developers who import any version of telnx, which automatically triggers execution without requiring user interaction or network inspection bypasses beyond the initial fetch from a command-and-control server described in earlier reports as part of TeamPCP's "When the Security Scanner Became the Weapon" campaign.
Key Points
-
1TeamPCP has compromised the Telnyx Python package on PyPI by uploading two malicious versions (4.87.1 and 4.87.2) to steal sensitive credentials.
-
2The malware utilizes a novel delivery method where it hides within WAV audio files using steganography, pulling payloads from command-and-control servers upon import without user interaction.
-
3This attack is part of an ongoing supply chain campaign by TeamPCP that previously targeted Trivy and litellm with similar credential-stealing techniques.
Developments
TeamPCP hackers compromised Telnyx's Python package on PyPI by uploading malicious versions containing credential-stealing malware hidden in an embedded WAV file. The attack, attributed to TeamPCP based on their prior exfiltration patterns and RSA keys used against Iranian systems like Aqua Security and LiteLLM, exploits the SDK's high popularity (over 740k monthly downloads) through stolen publishing credentials.
TeamPCP compromised two versions (4.87.1, 4.87.2) of Python's telnyx package published on March 27 by embedding credential harvesting malware within audio files (.WAV). This attack chain targets Windows and macOS systems to exfiltrate sensitive data via a C2 server at IP address ending in .[.]203:8080, with the PyPI project currently quarantined.
TeamPCP compromised the Telnyx Python SDK on PyPI using a new WAV audio steganography technique, deploying malicious versions 4.87.1/2 via stolen credentials to deliver payloads including persistent binaries for Windows or credential harvesters for Linux/macOS while exfiltrating data with an RSA-4096 public key matching the LiteLLM compromise pattern; concurrently, TeamPCP has partnered with Vect Ransomware and Breach according to this intelligence report.
Two versions of the Telnyx Python SDK were uploaded to PyPI containing malicious code that executes upon import without user interaction. The malware disguises itself as a valid audio file, downloading additional data from a command-and-control server and reconstructing an exploit using base64 decoding combined with XOR encryption rather than delivering typical payloads directly within the package files.
Endor Labs researchers confirmed that TeamPCP compromised Telnyx's PyPI credentials to publish backdoored versions 4.87.1 and 4.87.2 of the SDK between March 26–30, which delivered malware via encoded audio frames or runtime C2 requests without corresponding GitHub releases due to credential theft from a prior LiteLLM attack involving stolen PyPI tokens.